CIPP Components
About 8 months ago I’ve started a larger open source project called CIPP. CIPP is a M365 Management tool aimed at Managed Services Providers based on Azure Static Web Apps and a PowerShell backend. This blog shares some of the PowerShell code that’s used for the backend. CIPP is always looking for contributors on both the frontend and backend side so jump in if you’d like. You can find the Github project here.
Automating with PowerShell: Disabling Activity based timeout
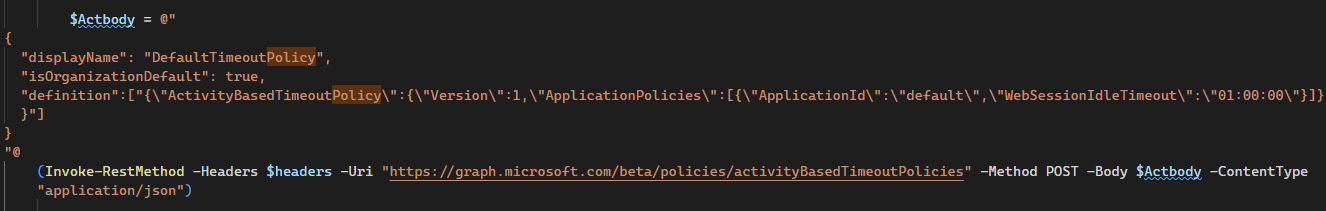
This was a feature request made some weeks ago for CIPP, and I liked it enough to immediately implement it. This script activates the Activity Based Timeout for M365 applications, that means if a user leaves their browser open for longer than 1 hour, you’ll get a little pop-up warning you that you’re going to be logged out. The script uses the Secure Application Model to connect to all your tenants and change their settings.
This script requires the ‘Policy.ReadWrite.ApplicationConfiguration’ permission, so make sure you have those set on your Secure Application Model app.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
|
#
$ApplicationId = 'AppID'
$ApplicationSecret = 'AppSecret'
$RefreshToken = "RefreshToken"
#
$credential = New-Object System.Management.Automation.PSCredential($ApplicationId, ($ApplicationSecret | ConvertTo-SecureString -AsPlainText -Force))
$graphToken = New-PartnerAccessToken -ApplicationId $ApplicationId -Credential $credential -RefreshToken $refreshToken -Scopes 'https://graph.microsoft.com/.default' -ServicePrincipal
Write-Host "Connecting to the Graph API to get all tenants." -ForegroundColor Green
$Contractheaders = @{ "Authorization" = "Bearer $($graphToken.accesstoken)" }
$Customers = (Invoke-RestMethod -Uri "https://graph.microsoft.com/v1.0/contracts?`$top=999" -Method GET -Headers $Contractheaders).value
foreach ($Customer in $Customers) {
try {
$body = @{
'resource' = 'https://graph.microsoft.com'
'client_id' = $ApplicationId
'client_secret' = $ApplicationSecret
'grant_type' = "client_credentials"
'scope' = "openid"
}
$ClientToken = Invoke-RestMethod -Method post -Uri "https://login.microsoftonline.com/$($customer.customerId)/oauth2/token" -Body $body -ErrorAction Stop
$headers = @{ "Authorization" = "Bearer $($ClientToken.access_token)" }
$Actbody = @"
{
"displayName": "DefaultTimeoutPolicy",
"isOrganizationDefault": true,
"definition":["{\"ActivityBasedTimeoutPolicy\":{\"Version\":1,\"ApplicationPolicies\":[{\"ApplicationId\":\"default\",\"WebSessionIdleTimeout\":\"01:00:00\"}]}}"]
}
"@
(Invoke-RestMethod -Headers $headers -Uri "https://graph.microsoft.com/beta/policies/activityBasedTimeoutPolicies" -Method POST -Body $Actbody -ContentType "application/json")
Write-Host "Enabled Activity Based Timeout for $($Customer.defaultdomainname)" -ForegroundColor Green
}
catch {
Write-Host "Could not enable Activity based timeout for $($customer.defaultdomainname): $($_.Exception.Message)" -ForegroundColor red
}
}
|
Update: Office Follina vulnerability
Right before I released this blog, a new issue arose for Microsoft Office that allows code execution. Thankfully, the workaround is easy and doesn’t seem to impact normal usage. Use the following script to mitigate the Office Folina issue:
1
2
3
4
5
6
7
8
9
10
11
|
$ENV:ActivateWorkaround = "Yes"
if($ENV:ActivateWorkaround -eq "Yes") {
New-PSDrive -PSProvider registry -Root HKEY_CLASSES_ROOT -Name HKCR
Set-Item -Path "HKCR:\ms-msdt" -Value "URL:ms-msdt_bak"
Rename-Item -Path "HKCR:\ms-msdt" -newName "ms-msdt_bak"
} else {
New-PSDrive -PSProvider registry -Root HKEY_CLASSES_ROOT -Name HKCR
Rename-Item -Path "HKCR:\ms-msdt_bak" -newName "ms-msdt"
Set-Item -Path "HKCR:\ms-msdt" -Value "URL:ms-msdt"
}
|
and that’s it! As always, Happy PowerShelling